In Salute to Our Veterans: How the Military Paved the Way to Modern Information Technology
The Military’s Role in Technological Advancements
By examining key eras and conflicts, it becomes evident that military needs have often spurred significant advancements that have later permeated civilian life. During World War II, for instance, the urgency to decipher enemy communications led to the development of early computing systems such as the Colossus and the ENIAC. These pioneering efforts laid the groundwork for modern computers, illustrating how military imperatives can catalyze technological progress.
Similarly, the Cold War era witnessed an intensification of research and development in information technology, driven by the strategic necessity to maintain technological superiority. Military funding and research during this period were instrumental in the creation of the ARPANET, which eventually evolved into the modern Internet. The need for secure and reliable communication systems during this time also led to advancements in satellite technology and cryptography, both of which are now integral to modern information infrastructures.
Moreover, the military’s focus on cybersecurity has had a lasting impact on the development of robust security measures in the digital age. Initiatives such as the creation of the National Security Agency (NSA) underscored the importance of protecting information and communication channels from cyber threats. These efforts have not only safeguarded national security but have also influenced the protocols and standards that govern cybersecurity practices across various sectors today.
In essence, the military’s role in technological advancements is both profound and far-reaching. By prioritizing research and development in information technology, the military has paved the way for many of the innovations that define our modern digital landscape. This introductory overview sets the stage for a deeper exploration of specific contributions in subsequent sections, highlighting the enduring legacy of military-driven technological progress.
Early Innovations: From ENIAC to ARPANET
The military has long been a driving force behind technological advancements, particularly in the field of information technology. One of the earliest and most significant contributions was the creation of the Electronic Numerical Integrator and Computer (ENIAC) during World War II. Commissioned by the United States Army, ENIAC was the first general-purpose electronic computer, designed to perform complex calculations more swiftly and accurately than ever before. It was initially developed to calculate artillery firing tables, but its capabilities extended far beyond military applications. ENIAC’s architecture, which included the use of vacuum tubes and a programmable structure, laid the foundation for subsequent developments in computing technology.
Following the success of ENIAC, the focus shifted towards creating a communication network that could withstand various forms of disruption. This led to the development of the Advanced Research Projects Agency Network (ARPANET) by the Advanced Research Projects Agency (ARPA) in the late 1960s. ARPANET was conceived as a means to facilitate resource sharing among researchers and enhance communication across different locations. It introduced the concept of packet switching, a method of data transmission that breaks down messages into smaller packets for more efficient routing. This innovation directly addressed the military’s need for a robust and resilient communication system, capable of maintaining functionality even in the event of partial network failures.
The impact of these military-driven innovations on civilian life cannot be overstated. ENIAC’s technological principles became the bedrock for the evolution of modern computers, influencing both hardware and software development. ARPANET, on the other hand, eventually evolved into the global internet, revolutionizing the way information is shared and accessed worldwide. These pioneering projects not only addressed immediate military needs but also spurred a cascade of technological advancements that have profoundly shaped contemporary information technology.
Communication and Encryption: Securing Information in the Digital Age
The military has long been at the forefront of advancing communication technologies and encryption methods, significantly shaping how information is transmitted and protected in the modern world. During World War II, the development of secure communication systems became paramount. The Enigma machine, used by the Germans, and its subsequent decryption by the Allies exemplify early efforts in cryptographic innovation. This pivotal point in history not only underscored the importance of encryption but also set the stage for future advancements in secure communications.
Post-war eras saw the military further pioneering in communication technology through the development of radio and satellite communications. The introduction of radio systems allowed for real-time communication over vast distances, a breakthrough that greatly enhanced military operations. This technology soon transitioned to civilian use, leading to the widespread availability of radio communication in various sectors, from emergency services to commercial broadcasting.
Satellite communication, another military innovation, revolutionized global connectivity. Initiatives such as the launch of the first communication satellites enabled secure, reliable long-distance communication, laying the groundwork for modern telecommunications infrastructure. Today, satellite technology is integral to global communications, supporting everything from GPS navigation to international broadcasting and internet services.
Encryption technologies have evolved significantly since the days of the Enigma machine. The military’s need for secure data transmission led to the development of advanced encryption standards (AES) and public-key cryptography. These methods ensure that sensitive information remains confidential and intact through cryptographic algorithms that protect data from unauthorized access. Modern-day cybersecurity protocols, heavily influenced by military advancements, now employ these encryption standards to safeguard digital communications against cyber threats.
In essence, the military’s contributions to communication and encryption technologies have been instrumental in shaping the digital landscape. The secure communication systems and encryption methods developed for defense purposes have seamlessly integrated into civilian applications, ensuring that information is transmitted and protected with unprecedented efficiency and security.
Spring Cleaning 2026: Why Your PC is Slow and How
If you feel like your computer has become noticeably slower since the start of 2026, you are not alone. Between…
Email Spoofing vs. Phishing: How to Protect Yourself
Is that email real? 🛡️ Learn the simple difference between spoofing and phishing to stay safe online….
Stop Spam Before It Hits Your Inbox: How to Use
Stop spam! 🦆 Learn to use DuckDuckGo Email Protection to block trackers and hide your address. Need secure setup? Goinsta…
Is Your Printer Holding Your Documents Hostage? Why You’re Being
Stop paying rent for the printer you bought! Learn how HP, Epson, and Canon use subscription fees to lock your…
Computer Security Alerts for March 2026: How to Stay Safe
Worried about fake Microsoft alerts, scam texts, suspicious pop-ups, or a slow computer? Learn what to do now and when…
Top 30 Most Common Passwords 2025: Is Yours on This
Most common passwords 2025 revealed—123456 still #1. Goinsta Repairs shows you how to stay safe with easy password fixes….
High-Severity Chrome Vulnerability Exposed AI Assistant to Hijacking – What
CVE-2026-0628: Gemini flaw let malicious extensions hijack AI assistant, access cameras, microphones & files. Get $139 emergency repair at Goinsta…
Are browser extensions safe?
Are browser extensions safe? Learn the biggest security risks, warning signs, and how GoInsta Repairs can remove suspicious extensions with…
Don’t Take the Bait: Your Complete Guide to Phishing Protection
Protect your family from phishing scams with simple email safety checks, what to do if you click a bad link…
Ransomware part II
Ransomware is malicious software that locks your files and demands payment to restore access….
Ransomware Recovery & Protection: Don’t Let Hackers Hold Your Data
Ransomware is malicious software that hijacks your data, blocks access to your device, and demands payment to get it back…
Locked Out? How to Protect Yourself from Ransomware and Sextortion
Cyber extortion happens when hackers break into your devices or network, then threaten to leak or destroy your data unless…
WhatsApp Blocked in Russia: What It Means for Secure Messaging
Russia blocks WhatsApp, tightening digital controls and impacting communication nationwide…
Update Roulette: A Repair Tech’s Take on How Microsoft Turned
At Goinsta Repairs, we pride ourselves on transparency with our customers. Today, we need to share something important: over the…
Quick Guide: Troubleshooting a Clogged Epson WorkForce Pro WF-7620 Printer
Epson WorkForce Pro WF-7620 printer troubleshooting…
Is Your Computer Slow? Here’s What’s Really Going On (And
Your computer lags—slow boot times, crawling apps, endless waits. Startup bloat, low RAM, old HDDs, and malware are usually to…
Best VPN for Everyday: Privacy, Speed & ISP Tracking Explained
A VPN hides your online activity from your ISP, boosts privacy, and only slightly impacts speed, making it a smart…
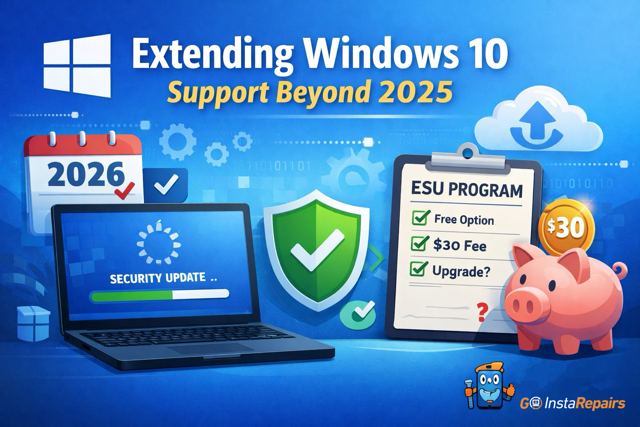
Windows 10 Support Ended: How to Get Extended Security Updates
Windows 10 support ended, but you can still get security updates in 2026….
Instagram Password Reset Email Alert: What You Need to Know
Instagram users are flooded with fake password reset emails. Learn what this 2026 scare means, how to spot scams, and…
Watch YouTube Without Ads, Learn How
With Brave configured correctly on your Mac, Windows, iPhone, or Android device, you’ll experience YouTube and YouTube Music with fewer…
The Future: Ongoing Military Contributions to IT and Cybersecurity
The relationship between the military and information technology has always been symbiotic, with each driving advancements that benefit the other. As we look to the future, the military continues to be at the forefront of pioneering innovations in information technology. Investments in artificial intelligence (AI) are a prime example of this ongoing commitment. The Department of Defense has been significantly funding AI research, focusing on developing autonomous systems, enhancing decision-making processes, and improving operational efficiency. These investments are not only enhancing military capabilities but also propelling the broader IT sector forward.
Quantum computing is another area where the military is making substantial strides. Recognizing the potential of quantum systems to revolutionize data processing and encryption, military research institutions are working on developing quantum technologies that promise unprecedented computational power and security. The advancements in quantum computing are expected to have wide-ranging implications, from secure communications to complex problem-solving in various fields.
In the realm of cybersecurity, the military’s role is indispensable. As cyber threats become more sophisticated, the military’s expertise in advanced cybersecurity measures is critical. Initiatives such as the Cyber Command and collaborations with private sector cybersecurity firms are fostering the development of cutting-edge technologies designed to protect national and global digital infrastructures. These efforts include the creation of resilient systems capable of withstanding cyberattacks and the development of new methodologies for threat detection and mitigation.
Collaborations between the military and civilian sectors are also driving significant technological breakthroughs. Public-private partnerships are facilitating the transfer of military innovations to civilian applications, accelerating technological progress across industries. These collaborations ensure that advancements in military technology can be leveraged to benefit society at large, from healthcare to transportation and beyond.
The enduring legacy of military contributions to information technology is profound. As the military continues to push the boundaries of IT and cybersecurity, it is clear that their innovations will shape the digital landscape for generations to come. The ongoing investment and collaboration in these fields underscore the importance of the military’s role in securing and advancing our digital future.