Different Types of Rootkits
In our previous post, we discussed what rootkits are and the damage they can cause to your device. Today, we will delve deeper into the types of rootkits, helping you understand how they operate and the potential risks they pose.
Bootloader Rootkits
(Bootkits)Bootloader rootkits, also known as bootkits, are a type of rootkit that infects the Master Boot Record (MBR) of a system. These rootkits target the initial code that is executed when a computer starts up, allowing them to gain control over the entire system from the moment it boots up.One example of a bootloader rootkit is the Alureon (or TDL) rootkit, which infected the MBR to gain persistence and control over infected systems. It was notorious for its ability to evade detection and removal by traditional antivirus software.Bootloader rootkits infect the MBR by replacing or modifying the legitimate bootloader code with their own malicious code. This allows them to execute their payload before the operating system even loads, making them difficult to detect and remove. By maintaining control over the bootloader, these rootkits can ensure their persistence on the system.Once a bootloader rootkit is successfully installed, it can perform various malicious activities such as disabling security software, stealing sensitive information, or even allowing remote access/control of the compromised system. The ability to manipulate the MBR gives bootloader rootkits significant power and control over the infected machine.A real-world case study highlighting the impact of bootloader rootkits is the Mebroot rootkit. It infected thousands of computers worldwide and was primarily used for financial fraud. Mebroot was capable of intercepting online banking transactions and altering them in real-time without being detected by the victim or security measures.Bootloader rootkits are a dangerous type of malware that infects the MBR and allows attackers to gain persistent control over compromised systems. Their ability to evade detection and maintain their presence makes them a significant threat to computer security. It is crucial to have robust security measures in place, including regular scanning for rootkit infections and keeping security software up to date, to protect against these stealthy attacks
Memory Rootkits
Memory rootkits are a type of rootkit that use memory-based techniques to hide malicious code in the system’s memory, especially in the kernel space. By being in such an important part of the operating system, memory rootkits can have full control and do their malicious activities without being easily found by normal security measures.
Here are some important things to think about when looking at memory rootkits:
Changing the Kernel Space: Memory rootkits use different methods to change the kernel space, where important system functions and processes are. This includes hooking system calls, changing kernel data structures, and fixing kernel code.
By changing the kernel, memory rootkits can go around security methods and stay on the infected system.
Hiding in System Memory: Unlike other types of rootkits that may be on disk or firmware, memory rootkits only exist in temporary memory. They do this by adding their bad code into running processes or by directly changing kernel memory. By doing this, they can’t be found by normal antivirus software that mostly looks at files on disk.
Finding and Stopping Memory Rootkits: Finding and getting rid of memory rootkits can be hard because they can hide in temporary memory. But there are special tools and methods for finding these hidden infections:
Memory Analysis: Good security tools can look at memory to find things that aren’t normal or seem suspicious because of a memory rootkit.
Checking for Changes: Regularly checking important system files to see if they’ve been changed without permission can help find changes caused by memory rootkits.
Watching for Changes: Watching how processes act and how they work with the kernel can show if there’s a memory rootkit around.
Unexpected changes to important things might mean there’s a hidden rootkit.
Real-World Examples: One big case where memory rootkits were used in a cyber attack is the Stuxnet worm. Stuxnet, a very tricky piece of bad software found in 2010, went for industrial control systems, mostly Iran’s nuclear program. It used memory rootkit methods to hide and change programmable logic controllers (PLCs) without anyone knowing.Memory rootkits are a big danger to system security because they can work secretly in the kernel space and get around normal finding methods. To lower the risk of getting a memory rootkit:Use good security tools that are made to look at memory and watch how things act.Keep important system programs and security software up to date with the newest fixes and changes. This can stop known problems that memory rootkits use
User Mode Rootkits
Application/user-mode rootkits are a type of rootkit that operate at a higher level than the kernel, targeting user processes and applications to achieve their malicious objectives. These rootkits leverage DLL (Dynamic Link Library) injection techniques to manipulate data and compromise system integrity.
Characteristics of application/user-mode rootkits:Higher-level operation: Unlike kernel rootkits that embed themselves deep within the operating system, application/user-mode rootkits operate at a higher level where user processes and applications reside. This allows them to target specific programs without directly modifying the underlying kernel.
DLL injection techniques: One common technique used by application/user-mode rootkits is DLL injection. By injecting malicious code into a legitimate DLL file, these rootkits can gain control over the targeted application and manipulate its behavior without detection.
Data manipulation: Application/user-mode rootkits often focus on manipulating data within the targeted processes. They can intercept and modify network traffic, steal sensitive information, or even modify the behavior of the compromised application to perform unauthorized actions.
Examples of applications commonly targeted by application/user-mode rootkits:
Web browsers: Rootkits may target web browsers like Chrome, Firefox, or Internet Explorer to intercept internet traffic, capture login credentials, or inject malicious advertisements.
Document editors: Popular document editing software such as Microsoft Word or Adobe Acrobat can be targeted by rootkits to manipulate documents, extract sensitive information, or even execute commands.
Media players: Rootkits may exploit media players like VLC or Windows Media Player to modify video playback, inject additional content, or steal media files.
Case study illustrating the impact of an application/user-mode rootkit on system integrity:In 2017, the “CCleaner” software was compromised by a sophisticated application/user-mode rootkit. CCleaner is a popular utility used for system optimization and cleaning. Attackers managed to inject malicious code into the official CCleaner software, which was unknowingly distributed to millions of users. The rootkit allowed attackers to collect sensitive information from infected systems, such as user credentials and system configurations. It also established a backdoor for remote access, enabling further malicious activities.
This incident highlights the danger posed by application/user-mode rootkits and the potential impact on system security. Even trusted software can be compromised, emphasizing the importance of staying vigilant and regularly updating security measures
Kernel Mode Rootkits
Kernel rootkits have special access to the operating system, allowing them to make hidden changes to both software and hardware. These rootkits can control software processes, drivers, and even take over the system remotely, posing serious risks to computer and network security.
Overview of Kernel RootkitsKernel rootkits are designed to work below the operating system’s core, giving them extensive control and the ability to hide effectively. By directly targeting the heart of the operating system, they can run harmful code and change important system functions without anyone noticing.
Techniques Used by Kernel Rootkits: These advanced rootkits use various methods to achieve their goals, including:
Direct Memory Modification: Kernel rootkits can change the computer’s memory directly to alter data structures or intercept function calls. This lets them hide or control how the system works.
Hooking System Calls: By intercepting and changing system calls made by programs running on the computer, kernel rootkits can control how information moves within the operating system.
Device Driver Manipulation: Kernel rootkits might tamper with device drivers to stay hidden and keep control over hardware parts.Real-life Examples Showing Dangers. One well-known example of a kernel rootkit is the Stuxnet worm. It used advanced techniques at the kernel level to get into industrial systems and control programmable logic controllers (PLCs). This complex attack showed just how much damage kernel rootkit infections can cause in critical infrastructure environments.
Another case is the Duqu malware. It used sneaky tactics at the kernel level to gather information from specific organizations without setting off any alarms in regular security systems. These examples highlight just how serious kernel rootkit infections can be in high-stakes situations, making it even more important to have strong security measures in place and stay alert against these threats.
Firmware Rootkits
Firmware rootkits are a type of malicious software that targets the firmware of a device, such as the BIOS (Basic Input/Output System) or UEFI (Unified Extensible Firmware Interface). These rootkits are designed to infect the firmware and remain persistent even after reformatting or reinstalling the operating system.
Definition and Characteristics: Firmware rootkits are highly stealthy and difficult to detect, as they operate at a level below the operating system. They can intercept and manipulate low-level system functions, making them extremely dangerous and persistent.Attack Vectors.
Firmware rootkits typically exploit vulnerabilities in the update process of the BIOS/UEFI firmware or use physical access to the hardware for infection. They can also be installed through malware that has already compromised the operating system.Infecting BIOS/UEFI ChipsThe process of infecting the BIOS/UEFI chips involves injecting malicious code into the firmware, which allows the rootkit to gain control over critical system functions and remain undetected by traditional security measures.
Survivability One of the most alarming aspects of firmware rootkits is their ability to survive reformatting and OS reinstalls. This makes them particularly dangerous, as they can maintain control over the compromised device even after attempts to remove them.
Notable Cases: There have been notable cases where firmware rootkits were used in sophisticated attacks. For example, the “LoJax” rootkit targeted UEFI firmware, allowing it to persist even after a complete system reinstallation.
Firmware rootkits pose a significant threat due to their ability to evade detection and persist on infected devices. Understanding their characteristics and attack vectors is crucial for implementing effective security measures against these insidious threats.
Hypervisor Rootkits
- Hypervisor rootkits are a unique and sophisticated type of rootkit that target the underlying virtualization layer, also known as the hypervisor or virtual machine monitor (VMM). These rootkits exploit the features and vulnerabilities of the hypervisor to carry out stealthy attacks and gain control over guest virtual machines (VMs).
Key Points about Hypervisor Rootkits
Definition and Unique Nature: Hypervisor rootkits operate at a lower level than other types of rootkits, allowing them to bypass traditional security measures. By compromising the hypervisor, they can intercept and manipulate system calls, memory access, and network traffic, all while remaining undetectable to the guest VMs.
Exploitation of Hypervisor Features: Hypervisor rootkits take advantage of various features provided by the hypervisor to carry out their malicious activities.
For example, they may use techniques like direct memory access (DMA) attacks to read or modify memory contents of other VMs. They can also leverage virtual machine introspection (VMI) capabilities to monitor and control the behavior of guest VMs.
Advanced Capabilities: Hypervisor rootkits are known for their advanced capabilities and stealthy behavior. They can hide their presence by intercepting and modifying system calls, altering memory structures, and evading detection by security software running within guest VMs. Some notorious examples of hypervisor rootkits include BluePill and VMBR. It is worth noting that hypervisor rootkits are relatively rare compared to other types of rootkits. However, they pose a significant threat in virtualized environments, where multiple VMs run on a single physical server. To protect against hypervisor rootkit attacks and maintain the integrity of your virtualized infrastructure, it is essential to implement strong security measures:
Regularly patch and update the hypervisor software. Monitor for any suspicious behavior or unauthorized changes within VMs. Use security tools specifically designed for virtualized environments.
By understanding the unique nature of hypervisor rootkits and taking appropriate security measures, organizations can mitigate the risk of these advanced attacks and ensure the integrity and security of their virtualized systems.
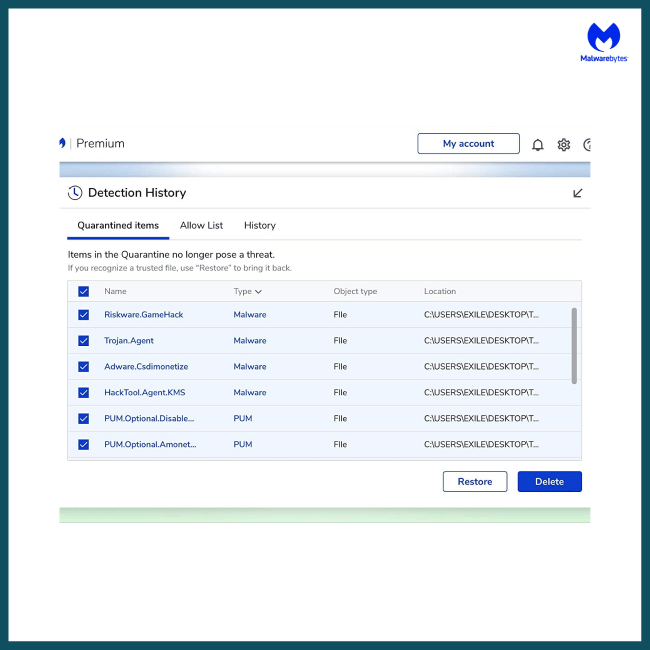
Detecting and Removing Rootkits. Rootkits can be difficult to detect and remove because they are designed to evade traditional security measures. Here are some important things to know:
- Challenges in Detection and Removal
Rootkits are skilled at hiding themselves within a system, making it hard for standard antivirus programs to find them. They can manipulate system processes and disguise themselves as critical system components, which makes it even more challenging to identify and eliminate them.
2. Specialized Tools and Techniques To effectively detect hidden rootkit infections, specialized tools and techniques are necessary.
These may include: Advanced rootkit scanners that use heuristic analysis, behavioral monitoring, and memory forensics to uncover the presence of rootkits within a system.
3. Comprehensive Antivirus Software
Using comprehensive antivirus software with built-in rootkit scanning capabilities is crucial. This ensures that the antivirus solution is able to recognize and remove rootkits, giving an extra layer of protection against these sneaky malware threats.
By understanding the challenges associated with detecting and removing rootkits, as well as utilizing specialized tools and comprehensive antivirus solutions, users can enhance their ability to safeguard their systems against these insidious threats.
Preventing Rootkit Infections
Preventing rootkit infections is crucial to safeguard your computer and personal information from unauthorized access and control. By following these preventive measures, you can significantly reduce the risk of rootkit infections:
Regular System Scanning: Conduct regular system scans using advanced threat scanners like Malwarebytes Premium.
These scanners are equipped with sophisticated algorithms that can detect hidden rootkit infections and other malware threats.
Exercise Caution with Downloads and Links:
- Be cautious when downloading files or clicking on links, especially from untrusted sources. Rootkits often spread through malicious downloads or phishing emails.
- Verify the authenticity of the source and ensure that the files or links are from trusted websites before proceeding.
- Keep OS and Security Software Up to Date:
- Keep your operating system and security software up to date to patch any vulnerabilities that rootkits may exploit.
Software developers constantly release updates with security fixes to address known vulnerabilities. Regularly check for updates and install them promptly.Following these preventive measures will strengthen your defenses against rootkit infections.
However, it’s important to note that rootkits are continuously evolving, and new variants may emerge that can evade detection by traditional security measures. Therefore, it is crucial to stay informed about the latest threats and employ comprehensive security solutions that offer advanced rootkit scanning capabilities.
By adopting a multi-layered security approach, which includes regular scanning, cautious online behavior, and keeping your system updated, you can significantly reduce the risk of falling victim to rootkit infections.
Remember, prevention is always better than dealing with the aftermath of an infection. Stay vigilant and prioritize the security of your devices to keep them safe from rootkit attacks.
Note: The information provided in this section is for general guidance purposes only. It is advisable to consult with cybersecurity professionals or follow the guidelines provided by reputable security organizations for specific recommendations tailored to your unique circumstances.
Conclusion
Rootkits are a dangerous form of malware that give unauthorized control of a computer to attackers. These advanced malware types embed deep into systems, making fundamental changes and hiding from traditional scanning techniques. They can be used for various malicious purposes, such as cryptojacking, identity theft, and network or device sabotage.
Throughout this article, we have explored the different types of rootkits and their unique characteristics:
- Bootloader rootkits that infect the Master Boot Record (MBR)
- Firmware rootkits that target BIOS/UEFI chips
- Kernel rootkits that manipulate software processes
- Memory rootkits that hide malicious code in system memory.
Each type poses its own set of challenges and risks.
We have discussed the importance of detecting and removing rootkits, which can be challenging due to their ability to evade traditional security measures. However, there are various techniques and specialized tools available for detecting hidden rootkit infections. threats.
FAQs (Frequently Asked Questions)
What are bootloader rootkits (bootkits)?
Bootloader rootkits are a type of malware that infects the Master Boot Record (MBR) of a system, allowing them to maintain persistence and control over the boot process. They can be used to launch malicious software or hide the presence of other malware.
How do bootloader rootkits infect the Master Boot Record (MBR) and maintain persistence?
Bootloader rootkits infect the MBR by replacing legitimate bootloader code with their own malicious code. They maintain persistence by ensuring that their code is executed every time the system boots up, allowing them to remain undetected and in control of the system.
Can you provide a real-world incident showcasing the impact of bootloader rootkits?
One notable incident involving a bootloader rootkit is the Stuxnet worm, which used a combination of MBR infection and firmware rootkit techniques to target industrial control systems, causing significant damage to Iran’s nuclear program.
What are firmware rootkits and how do they ensure survivability?
Firmware rootkits are designed to infect the BIOS/UEFI chips in devices, allowing them to survive even after reformatting or reinstalling the operating system. They achieve this by embedding themselves within the hardware, making them extremely difficult to detect and remove.
Are there any notable cases where firmware rootkits were used for sophisticated attacks?
Yes, one such case is the Equation Group’s use of firmware rootkits to persistently infect hard drive firmware. This allowed them to create a highly sophisticated and stealthy malware platform capable of evading traditional security measures.
What are kernel rootkits and how do they gain remote access?
Kernel rootkits are designed to manipulate software processes and drivers at the kernel level, granting them privileged access to the operating system. They can gain remote access by exploiting vulnerabilities in network protocols or installing backdoor mechanisms for remote control.





![AVG Ultimate 2023 1 Year- 10 Devices [Download] + Free remote Installation](https://goinstarepairs.com/wp-content/uploads/2023/01/img_0160-650x650.png)